CMMC Compliance Overview
The Cybersecurity Maturity Model Certification (CMMC) is a proactive measure first introduced in January 2020 and enacted later that year by the United States Department of Defense (DoD) to protect companies in the Defense Industrial Base (DIB) from cybersecurity theft. While the number of threats to cybersecurity has been trending upwards in recent years, the onset of the COVID-19 pandemic saw a 600% increase in cybercrime alone. Not only that, but these attacks are becoming more and more sophisticated, targeting supply chains and the sensitive data that moves along them across a number of industries.
How did the CMMC come to be?
In order to protect the controlled unclassified information (CUI) that resides within the DIB — which are companies that support the DoD through research, development, design, production, delivery, and maintenance of military weapons, systems, and other products — the DoD sought to create a standardized certification process for vendors’ cybersecurity infrastructures. This would ensure their processes and safeguards were up to par and at the bare minimum, suitable enough to protect CUI from the ever-increasing risk of cyber theft.
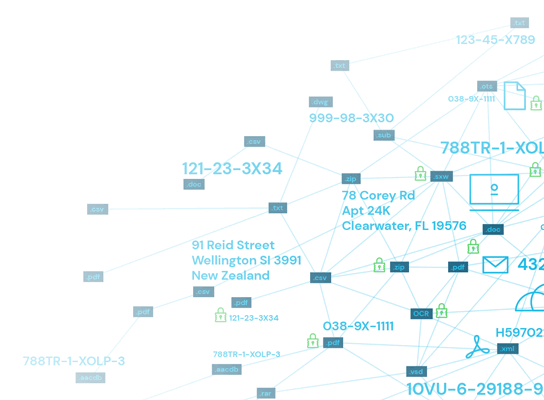
What information does the CMMC control?
The CMMC seeks to eliminate or reduce information theft of CUI. CUI can be any information created or owned by the government, or by another entity on behalf of the government, such as DIB vendors and contractors. The definition of data in the context of CUI is broad. It can include:
- Financial data
- Legal data
- Intelligence
- Infrastructure data
- Export controls
Who must be CMMC certified?
CMMC compliance is mandatory for any organization, contractor, or vendor in the defense supply chain. In addition to those working with the DoD directly, this also includes subcontractors who support the fulfillment of those contracts.
Under the CMMC, there are five levels of security requirements companies should work to meet, but at the bare minimum, they must meet Level 1 requirements, or those demonstrating basic cyber hygiene. Certain jobs call for higher levels of cybersecurity, and thus higher levels of certification. Certifications are good for three years, and the idea is to be recertified after those three years at the next level. These certification levels are:
- Level 1: Contractors must implement 17 controls of NIST 800-171 rev1. This aims to protect federal contract information and demonstrates basic cyber hygiene.
- Level 2: Contractors must implement 48 more controls from NIST SP 800-171 rev1, as well as seven other cybersecurity practices to support intermediate cyber hygiene.
- Level 3: Contractors must implement the remaining 45 controls of NIST SP 800-171 rev1, plus 13 additional practices. This is the level where an organization demonstrates that they have a security infrastructure equipped to handle CUI.
- Level 4: Contractors must implement all the controls mentioned in Levels 1 through 3, as well as 11 new controls from NIST 800-171 Rev2 and 15 additional ones.
- Level 5: Contractors must implement the remaining four controls of NIST 800-171 Rev2, as well as 11 additional controls for cybersecurity, to demonstrate the most advanced cybersecurity program. This level of certification is rare, but contractors that do need to obtain it will likely be working with highly valuable CUI that faces ongoing threats from foreign nations.
In November 2021, the DoD proposed improvements to the CMMC, including better alignment with the widely implemented National Institute of Standards and Technology (NIST) cybersecurity measures, that consolidate the five levels of security into three. Level 1 remains the same, while Levels 2 and 3 from CMMC 1.0 make up Level 2 of CMMC 2.0, and Levels 4 and 5 of CMMC 1.0 make up Level 3 of CMMC 2.0.
Per the DoD, these enhancements aim to:
- Ensure accountability for companies to implement cybersecurity standards while minimizing barriers to compliance with DoD requirements;
- Instill a collaborative culture of cybersecurity and cyber resilience; and
- Enhance public trust in the CMMC ecosystem, while increasing overall ease of execution.
When do I need to get CMMC certified?
The DoD launched a phased rollout of CMMC regulations on Nov. 30, 2020 and expects CMMC regulations to be applied across all contracts by Oct. 1, 2025. The pilot program focuses on mid-sized contractors that the DoD expects will process or store CUI according to the CMMC’s Level 3 security protocols. A small number of organizations with larger contracts may be subject to CMMC Level 4 and 5 security protocols during this period.
Even for a Level 1 certification, meeting the requirements is no easy feat. The controls will likely take time to implement, and when the time comes to be certified, you won’t simply be evaluated for having the required security controls in place. These controls must really be ingrained within your organization’s operations and processes, fully developed and functional — mature, if you will. And maturity takes time, thus, it’s better to get started on the certification process sooner rather than later.
How to become CMMC-compliant
Get help from a CMMC consultant
CMMC consultants — also called Managed Security Service Providers (MSSP) — specialize in compliance for DoD contractors. They can assess an organization’s security infrastructure to either ensure it meets the requirements of CMMC levels 1-5 or help it get there. If your organization fails to meet the requirements outlined in the CMMC, the MSSP will put together a plan of action for system security complete with milestones. The DoD requires this documentation to prove that your organization is taking steps towards compliance.
A plan of action will essentially lay out all the technological adjustments and additions your organization needs to implement to meet your nearest CMMC level. The insights offered by consultants could range from minor updates to complete overhauls of your organization’s IT infrastructure. Regardless, consulting groups will make suggestions that, if followed, will leave your organization in the best position to pass inspection from CMMC auditors.
It’s worth noting that the certification process alone averages about six months in length, so organizations should seek to achieve CMMC compliance with plenty of time and patience on their sides.
Implement automated sensitive data classification and remediation tools
Automated data classification and data remediation can help make your organization’s transition into CMMC compliance more efficient, while also reducing the human resources needed for execution and removing the risk of human error.
After discovering a record or file containing CUI, data classification software can categorize it based on preset or custom criteria. This can include level of sensitivity, as well as the compliance regulation(s) that data is subject to, so the appropriate and compliant safeguards can be applied to it. Once it’s been classified, a remediation tool can help to maintain the hygiene of the data itself, as outdated or inaccurate information creates security vulnerabilities that CMMC controls may not be able to protect against. If a vulnerability within the CUI itself allows for it to be accessed and stolen, the breached organization faces a violation of compliance (and its accompanying penalties) plus the deep ramifications of such valuable information being in malicious hands.
Receive official CMMC accreditation
Naturally, contractors and vendors can’t just declare themselves CMMC certified because they implemented the controls required by a certain level. They must be officially accredited, a process involving the following three parties:
The CMMC Accreditation Body (CMMC-AB) is an agency independent of the DoD that spearheads CMMC assessments, certifications, training, and accreditations. The CMMC-AB is responsible for certifying the certifiers — CMMC Third-Party Assessment Organizations and Certified Assessors — and setting the criteria for accreditation.
CMMC Third-Party Assessment Organizations (C3PAOs) are entities accredited by the CMMC-AB to evaluate the cybersecurity practices and infrastructures of DoD contractors seeking certification. As mentioned, these certifications are effective for three years, after which a contractor would either need to be recertified at its current level, or ideally, certified in the next level. These third-party vendors can be found on the CMMC-AB Marketplace.
Certified Assessors are the individuals actually conducting the audits and awarding accreditations. They work for a C3PAO and certify based on guidelines put forth by the CMMC-AB. Certified Assessors also must be certified by the CMMC-AB themselves, and they don’t handle certifications for all levels. Instead, Certified Assessors will specialize in a specific CMMC level and only evaluate contractors seeking that level of certification.
The bottom line on CMMC compliance
If you are a contractor or subcontractor involved with any part of the U.S. Department of Defense’s supply chain, being CMMC-compliant isn’t something to aspire to — it’s a must. With sophisticated cybersecurity threats constantly emerging and targeting the DoD’s sensitive CUI, any entity that engages in work with the DoD is required to demonstrate a basic level of cybersecurity hygiene. Over time, as security controls mature and new ones get implemented, the idea is to have an impenetrable protective framework that keeps the most valuable and potentially harmful information out of the wrong hands.
While the CMMC is relatively new and taking a gradual approach to its rollout, working your way to certification sooner rather than later can ensure you implement security controls with the time and attention they need to mature into robust safeguards that will no doubt guarantee your organization its certification and ongoing compliance.
