Data Remediation
- What is data remediation?
- Data remediation terminology
- Stages of data remediation
- Business benefits of data remediation
- When is data remediation necessary?
- What prevents organizations from performing data remediation?
- How to prepare your business for data remediation
- Explore Spirion data management tools
Security teams are responsible for making accurate decisions when it comes to the protection, hygiene and compliance of their company’s data — which is no easy feat, especially with the volume of unstructured data that exists. Unstructured data is information that is not easily searchable and accounts for most of the data organizations create on a daily basis. The high volume of unstructured data that an organization collects can end up creating functional, financial and regulatory issues.
An overload of data can be overwhelming for any organization’s security team. For one, it is difficult for internal teams to work efficiently if they don’t know where the data they need to work with is, and if they are unsure that the data at hand is accurate and clean. From a cost-efficiency perspective, organizations are likely to overspend on their data storage by hanging on to unnecessary data or by storing all types of data in one place regardless of its sensitivity level. And finally, without a complete view of your organization’s data or determined action steps for “dirty” or sensitive data, your organization could be at legal compliance risk.
This is where data remediation plays a central role in ensuring that a company’s data network is secure, and that they are operating at peak standards.
What is data remediation?
Data remediation is the process of cleansing, organizing and migrating data so that it’s properly protected and best serves its intended purpose. There is a misconception that data remediation simply means deleting business data that is no longer needed. It’s important to remember that the key word “remediation” derives from the word “remedy,” which is to correct a mistake. Since the core initiative is to correct data, the data remediation process typically involves replacing, modifying, cleansing or deleting any “dirty” data.
Data remediation terminology
As you explore the data remediation process, you will come across unique terminology. These are common terms related to data remediation that you should get acquainted with.
- Data Migration – The process of moving data between two or more systems, data formats or servers.
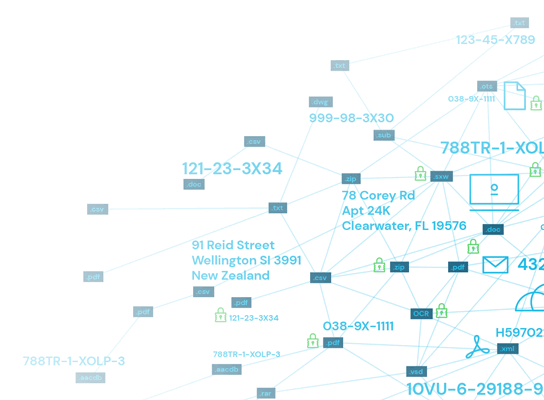
- Data Discovery – A manual or automated process of searching for patterns in data sets to identify structured and unstructured data in an organization’s systems.
- ROT – An acronym that stands for redundant, obsolete and trivial data. According to the Association for Intelligent Information Management, ROT data accounts for nearly 80 percent of the unstructured data that is beyond its recommended retention period and no longer useful to an organization.
- Dark Data – Any information that businesses collect, process and store, but do not use for other purposes. Some examples include customer call records, raw survey data or email correspondences. Often, the storing and securing of this type of data incurs more expense and sometimes even greater risk than it does value.
- Dirty Data – Data that damages the integrity of the organization’s complete dataset. This can include data that is unnecessarily duplicated, outdated, incomplete or inaccurate.
- Data Overload – This is when an organization has acquired too much data, including low-quality or dark data. Data overload makes the tasks of identifying, classifying and remediating data laborious.
- Data Cleansing – Transforming data in its native state to a predefined standardized format.
- Data Governance – Management of the availability, usability, integrity and security of the data stored within an organization.
Stages of data remediation
Data remediation is an involved process. After all, it’s more than simply purging your organization’s systems of dirty data. It requires knowledgeable assessment on how to most effectively resolve unclean data.
Assessment
Before you take any action on your company’s data, you need to have a complete understanding of the data you possess. How valuable is this data to the company? Is this data sensitive? Does this data actually require specialized storage, or is it trivial information? Identifying the quantity and type of data you’re dealing with, even if it’s just a ballpark estimate to start, will help your team get a general sense of how much time and resources need to be dedicated for successful data remediation.
Organizing and segmentation
Not all data is created equally, which means that not all pieces of data require the same level of protection or storage features. For instance, it isn’t cost-efficient for a company to store all data, ranging from information that is publicly facing to sensitive data, all in the same high-security vault. This is why organizing and creating segments based on the information’s purpose is critical during the data remediation process.
Accessibility is a big factor to consider when it comes to segmenting data. There’s data that needs to be easily accessed by team members for day-to-day tasks, and then there’s data that needs to have higher security measures for legal or regulatory purposes. For the data that needs to be regularly accessed, a cloud-based storage platform makes sense. For sensitive data that has greater privacy requirements, organizations will probably want to separate that data and store it on another platform with advanced security features. This is one example of two segments an organization may create.
Another important consideration factor when creating segments is determining which historical data is essential to business operations and needs to be stored in an archive system versus data that can be safely deleted. ROT data is a good example of information that can be safely deleted, while other business records that are still within a recommended retention period could be stored in an archive system.
Indexation and classification
Once your data is segmented, you can move onto indexing and classification. These steps build off of the data segments you have created and helps you determine action steps. In this step, organizations will focus on segments containing non-ROT data and classify the level of sensitivity of this remaining data.
Regulated data like personally identifiable information (PII), personal health information (PHI) and financial information will need to be classified with the company’s terminology for the highest degree of sensitivity. “Restricted data” is a common sensitive data classification term for data of this nature. Then, there’s unregulated and unstructured data that may consider sensitive information, and could be classified as internal, confidential or restricted data, depending on its level of sensitivity.
Migrating
If an organization’s end goal is to consolidate their data into a new, cleansed storage environment, then migration is an essential step in the data remediation process. A common scenario is an organization who needs to find a new secure location for storing data because their legacy system has reached its end of life. Some organizations may also prefer moving their data to cloud-based platforms, like SharePoint or Office 365, so that information is more accessible for their internal teams.
Data cleansing
The final task for your organization’s data may not always involve migration. There may be other actions better suited for the data depending on what segmentation group it falls under and its classification. A few vital actions that a team may proceed with include shredding, redacting, quarantining, ACL removal and script execution to clean up data.
Business benefits of data remediation
Data remediation is a big effort, but it comes with big benefits for businesses as well. These are the top benefits that most organizations realize after data remediation.
- Reduced data storage costs — Although data remediation isn’t solely about deletion of data, it is a common remediation action and less data means less storage required. Additionally, many organizations realize that they have lumped trivial information in the same high-security storage platform for sensitive information, instead of only paying for the storage space that’s actually necessary.
- Protection for unstructured sensitive data — Once sensitive data is discovered and classified, remediation is where you determine and execute the actions that mitigate risk. This could look like finding a secure area to store sensitive data or deleting what is necessary from a compliance perspective.
- Reduced sensitive data footprint — By removing sensitive data that is beyond its recommended retention period and is necessary for compliance, you’ve reduced your organization’s sensitive data footprint and decreased risk of potential data breaches or leaks of highly sensitive data.
- Adherence to compliance laws and regulations — Hanging on to data that is beyond its recommended retention period can create greater risks. By cleaning up data, your organization reduces data exposure which supports compliance initiatives.
- Increased staff productivity — Data that your team uses should be available, usable and trustworthy. By streamlining your organization’s network with data remediation, information should be easier to find and usable for its intended purpose.
- Minimized cyberattack risks — By continuously engaging in data remediation, your organization is proactively minimizing data loss risks and potential financial or reputational damage of successful cyberattacks.
- Improved overall data security — Data remediation and data governance work hand in hand. In order to properly remediate data, your organization will need to establish data governance policies, which is significant for the overall management and protection of your organization’s data.
When is data remediation necessary?
Data remediation is an essential process for any organization to ensure optimal hygiene and legal compliance standing. It’s recommended for any company to stay consistent with data remediation, but there are some specific instances that may occur and become a strong driver for prioritizing data remediation.
Business changes
If a company has changed software or systems they use, or even moved to a new office or data center location, that is a case to buckle down on data remediation immediately. Sometimes companies switch to new softwares or systems because they need to phase out their legacy system that has reached its end of life. Change of any kind is rarely ever 100 percent smooth, and data could become corrupted or exposed during the shuffle of changing environments — whether it be digital or physical.
Another event that may be a motivator to conduct data remediation is a company merger or acquisition. Similar to a change in systems or location, the organization is likely experiencing major changes in leadership, staff, work processes, and more. Even if your organization’s data is pristine, you cannot say the same about the new company that is joining forces with you until you take the time to discover, classify and, eventually, remediate data.
Laws and regulations
Newly enacted laws or regulations, either on a state or federal level, could be another major driver for data remediation. Data privacy and protection laws are continuously being updated and improved upon, like the more recent California Consumer Protection Act of 2018 (CCPA). Sometimes new policies may be enacted by the leadership team at your organization as well.
Human error
Drivers for data remediation aren’t always necessarily as grand as a new business acquisition or legal regulation. Sometimes, instances as simple as human error can be a catalyst for data remediation. For instance, let’s say that your organization discovers one of its employees has unintentionally downloaded sensitive corporate data on their personal mobile phone. Or, perhaps a couple of employees accidentally opened up a malicious spam email. Actions as innocent as these examples could put the integrity of your organization’s data at risk and is cause for immediately taking action with data remediation.
More examples of scenarios that may trigger the need to remediate data include:
- Preparing legal documentation for an investor portfolio sale
- Eliminating personally identifiable information (PII) or personal healthcare information (PHI)
- Enterprise resource planning (ERP)
- Master Data Management (MDM) implementation
What prevents organizations from performing data remediation?
As important as data remediation is, many organizations bypass this process. Oftentimes, other activities like data migration may seem to be an adequate replacement for the exhaustive task of comprehensive data remediation. However, projects like that are typically one-time endeavors that aren’t a continuous effort of cleansing and validating an organization’s data.
Lack of information
A common reason that organizations ignore data remediation is a lack of information about what, where, how and why data is stored in the company. An organization may not even realize the expanse of data they have collected or where it’s even stored. Awareness is a common issue, and since such a large percentage of sensitive data falls under the unstructured category, locating and awareness of all of this data is difficult. It’s recommended that organizations, especially those who belong to industries that interact with high volumes of sensitive data (like the medical, financial or education industries), regularly perform sensitive data discovery and data classification to prepare for data remediation. All of these steps are essential to a healthy data lifecycle and depend on one another to keep a company’s data security in good standing.
Fear of deleting data
Another factor that may prevent an organization from getting started with data remediation is a fear of deleting data. The permanency of the action can be intimidating, and some businesses may be concerned that they may need the data at hand at some point in the future. However, hanging on to unnecessary data, or leaving dirty data unmodified or uncleansed, can pose greater risk to an organization — especially when it comes to compliance laws and regulations.
Unclear data ownership
Lastly, some organizations may not have established clear data ownership. If there aren’t clear roles and responsibilities for each member of your organization’s security team, then important tasks like data remediation can easily slip through the cracks. It’s essential to determine each person’s key responsibilities when it comes to maintaining data security, and to make those duties transparent across the organization so that everyone knows who to turn to for specific security questions, and to keep the team accountable.
How to prepare your business for data remediation
Whether you’ve put data remediation on the back-burner or are realizing for the first time the benefits of steady data remediation, here are several steps your team should take to prepare for data remediation.
- Data remediation teams – First, create data remediation teams. In doing this, your organization will need to establish data ownership roles and responsibilities, so everyone on your security team knows how they are contributing and who to go for with questions or concerns.
- Data governance policies – From there, you will need to establish company policies that enforce data governance. An effective data governance plan will ensure that the company’s data is trustworthy and does not get misused. Typically, data governance is a process largely based on the company’s internal data standards and policies that control data usage in order to maintain the availability, usability, integrity and security of data.
- Prioritize data remediation areas – Once you have your organization’s policies and data remediation team assembled, you should begin prioritizing which areas may require more immediate data remediation. If any of the drivers we mentioned above have occurred, such as your organization switching to a new platform or an urgent need to eliminate PII, those are great starting points for prioritizing the order of business areas that need data remediation.
- Budget for data-related issues – After compiling a prioritized list, it’s time to budget for any data-related issues that may occur during the remediation process. This includes estimating the hours of labor for the process and factoring in costs for any special tools that may be needed for remediation.
- Discuss data remediation expectations – Either after or alongside the budgeting process, your team should sit down and discuss general expectations of the data remediation process. Are there any types of sensitive data your team expects to find? Are there any recent overarching data security issues or changes that could have an impact or effect on the remediation process? During the discussion, important details may be brought to light for the team that only one person was aware of and help the team reach success.
- Track progress and ROI – All company’s want to understand their ROI on big projects and initiatives, and this applies to data security measures too. Your organization’s IT data security lead should create a progress reporting mechanism that can inform company stakeholders on the data remediation progress, including key performance indicators like amount of issues resolved or how resolved issues translate into money and risk saved.
Explore Spirion data management tools
Organizations create data every day, and oftentimes sensitive information is hidden in unstructured or unregulated data. This is why greater volumes of data typically equate to increased risks, and why organizations cannot ignore data remediation. It is, after all, the process that resolves any dirty data or security gaps in your organization’s network.
There are several steps to the data remediation process but it does not need to be a stressful or overly time-consuming endeavor for your company’s IT security team. With the proper tools to aid in data discovery, classification and remediation, your team can save time and even automate a remediation workflow. Spirion has developed the solution with the highest accuracy in the market: Sensitive Data Platform.
Both solutions are equipped with leading edge data discovery, classification and remediation tools that work for on-premise endpoints, cloud repositories or remote servers at enterprise scale. Data Privacy Manager has more robust features, but both of these solutions include data discovery, classification and remediation tools to ensure that your organization’s data is secure and upholds accurate and timely compliance.
