The Gramm–Leach–Bliley Act (GLBA)
In an era when digitization is rapidly advancing, technology is changing the way organizations and consumers interact. Money is becoming more virtualized, and financial transactions more fluid. Keeping up with the compliance requirements of rapidly changing data privacy regulations can be a challenge. Still, there’s one specific federal law that has been in effect for more than two decades and demands compliance: the Gramm-Leach-Bliley Act, or GLBA.
What is GLBA?
The Gramm-Leach-Bliley Act was enacted in 1999 and regulates how businesses handle customers’ and prospective customers’ personal information when providing financial products or services.
Many organizations make the mistake of assuming that the GLBA is only applicable to narrowly defined financial institutions, such as banks and credit unions, or companies that solely depend on providing financial products and services, like credit card companies, insurance companies, or investment brokers.
However, the act applies to any institution that provides financial products or services, including:
- Check-cashing businesses
- Credit reporting agencies
- Courier services
- Financial advisors
- Financial advisors
- Mortgage brokers
- Non-bank lenders
- Payday lenders
- Personal property or real estate appraisers
- Professional tax preparers (like CPA firms)
- Stores that offer their own credit card or financing programs
Who Does the GLBA Protect?
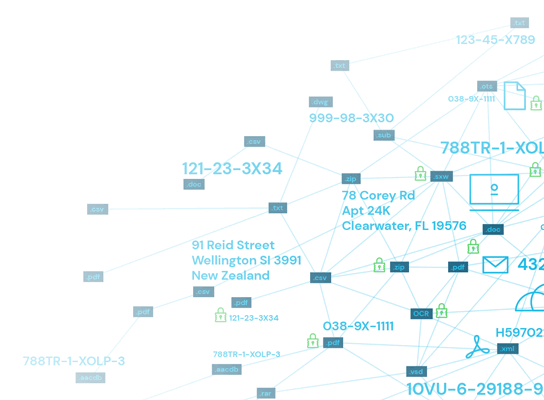
The GLBA specifically protects Nonpublic Personal Information (NPI), which can include any or all of the following:
- Information provided on an application, such as an individual’s name, address, income, social security number or nonpublic phone number.
- Information obtained from a transaction, such as an individual’s identification as a customer or consumer of a company, their account numbers, loan or deposit balances, credit or debit card purchases, and payment history.
- Information obtained via the not-publically-available data collection through the act of providing a financial product or service (for example, obtained from a court record or a consumer report).
How do Financial Institutions Comply with the Requirements of GLBA
There are three separate requirement sections in the GLBA. Each section is distinct and applies to different aspects of data collection, use or sharing, including issues related to disclosure practices and data privacy, sharing, storage, and security.
Safeguards rule
The Safeguards Rule mandates financial institutions to set up systems to protect private financial information. These systems must be internal and external, encompassing vendors and other third parties who may gain access to sensitive information through their own relationship with the financial institution.
Safeguards must include a written information security plan that describes in detail the measures the institution is taking to protect customers’ sensitive information. This plan must cover the following:
- One or more employees must be specifically designated to coordinate the information security program.
- Potential risks to the security and privacy of customer information in each relevant area of the company’s operation must be identified and assessed.
- An evaluation of how effective existing safeguards are for controlling these risks.
- A detailed safeguards program must be designed, implemented, and regularly monitored and tested.
- Service providers capable of maintaining appropriate safeguards may be selected. All contracts with such third parties must include language requiring them to maintain such safeguards and handle customer information to be overseen.
- The entire program must be promptly evaluated and adjusted when relevant circumstances arise. These could include changes in the institution’s business or operations or unsatisfactory results from a monitoring effort or security test.
Implementing data compliance tools can make it easier for designated persons to coordinate the information security plan. When all pieces of data are classified based on their sensitivity level, it makes it easier for your appointed team to assess and mitigate risks as appropriate. Sensitive data discovery tools also ensure there are no gaps in sensitive data coverage and protection.
Financial privacy rule
The Financial Privacy Rule is designed to guide the disclosure of a financial institution’s data privacy policies and practices.
To properly comply with this rule, it is important to understand that the GLBA does not allow for the terms “customer” and “consumer” to be used interchangeably. The consumer is the broader category, and customers are a subset. Not all consumers are customers, but all customers can also be defined as consumers.
For example, a consumer can be any individual who obtains, has obtained, or has applied to obtain a financial product or service. They can have interacted with any financial institution as defined under the GLBA, and can have interacted for purposes related to themselves as individuals, their family, or their household. This also includes legal representatives of individuals acting on their behalf.
Typical consumer relationships consist of a point of service action:
- Applying for a loan (regardless of whether or not it’s accepted)
- Obtaining cash from a non-account-holder ATM (counts even if the action is repeated)
- Arranging or making a wire transfer
- Using a check-cashing company to cash a check (counts even if the action is repeated)
In contrast, customers perform repeated actions that create a continuing relationship with the financial institution (beyond simple one-off transactions like ATM withdrawals or check cashing.)
Typical customer relationships consist of interactions with the same financial institution, often as part of what can be expected to remain an ongoing pattern over time:
- Opening a credit card account (with any institution that offers one)
- Obtaining a mortgage, vehicle, or payday loan
- Leasing a car from a car dealership
- Using a mortgage broker to obtain financing
- Using the services of a tax preparer or investment advisor
Former customers, such as someone who arranged for a loan through one company but has their loan serviced by another company, are now simply consumers in relation to the original lender and current customers of the current loan servicer.
The rule requires that such businesses provide each customer and/or consumer with a privacy notice at multiple touchpoints.
For customers, this begins when the customer relationship is established and is repeated annually thereafter. For consumers, it is whenever NPI is going to be disclosed to a non-affiliated third party (outside of certain exceptions.)
This privacy notice from the organization must:
- Explain what information will be collected about the customer/consumer
- Disclose where that information will be shared
- Detail how that information will be used
- Describe how that information will be protected from data breaches and other malicious threats
This notice must also lay out a consumer’s right to opt-out of the information shared with unaffiliated parties. This is required to remain in compliance with the provisions of the Fair Credit Reporting Act.
Any unaffiliated parties that receive nonpublic information must be held to the consumer’s acceptance terms as dictated by the original relationship agreement.
Data discovery and persistent Data Classification and tool capabilities can help make following this rule easier by quickly discovering and classifying sensitive data like NPI. Since DPM tools leverage advanced algorithms and machine learning, they can discover and classify sensitive data rapidly with a higher accuracy rate than if those tasks were performed manually—since teams always need to account for potential human error with manual work. By providing an overview of the data landscape, where a data breach could occur, a DPM could reduce an organization’s liability by avoiding miscategorized data.
Pretexting provisions
Finally, Pretexting Provisions preclude the access of private information under false pretexts or pretenses. The GLBA explicitly forbids obtaining/attempting to obtain or attempting/causing to disclose sensitive customer information held by a financial institution by “false pretenses or deception.”
Employees of financial institutions are often targeted by bad actors who try to trick them into disclosing or providing access to information through social engineering. The best way to comply with the GLBA concerning the Pretexting Provisions is to maintain a culture of employee education and awareness around social engineering tactics.
Examples of social engineering include phishing, using phony websites for data collection purposes, or contacting an employee and pretending to be a vendor, superior, executive, or authorized third party seeking information. By instituting a zero-trust policy and setting up multiple steps for request authentication and authorization, customer data can be protected.
Again, data classification helps to clearly identify all data in a system that could fall under the protection of these provisions and help prevent such data from being inadvertently exposed.
Creating a GLBA risk assessment template
One of the best ways for an organization to ensure compliance with the GLBA is to perform regular risk assessments. These assessments allow your organization to proactively address vulnerabilities in order to protect customer data while fulfilling requirements for GLBA compliance.
The specific needs of your organization will determine your threats as well as the parties responsible for resolution and other follow-up actions. However, here are some general guidelines you should include in your risk assessment to ensure you are adequately prepared for potential threats or audits.
These assessments are often most helpful when laid out visually in either a spreadsheet or some form of visual risk assessment matrix.
Data Breach Threat identification
The primary columns in your risk assessment template should include information related to the threats your organization is facing. Remember, the objectives of a GLBA risk assessment should always be focused on GLBA regulations. Maintain focus on these threats to ensure the assessment does not go beyond scope.
Designate the risks your customer data faces
Risks to your organization and the customer data it collects can be either internal or external. Look for broad areas of concern including existing physical and electronic security measures, security operations, response procedures, and all other potentially disruptive events. List these threats by name with one item per row, broken down to a level granular enough to be actionable.
Identify the parties most likely to be affected by a data breach
One of the columns on your template should include a list of the parties most affected by each threat. By organizing information in this way, you will be better able to identify possible actions which can be taken.
Note that individual threats may affect multiple parties, and risks for each party may be different. Consider breaking this information down even further in order to identify additional steps that may need to be taken.
Risk ratings
Once risks have been identified, they need to be qualitatively assessed in order to determine priority. While all threats could ideally be addressed simultaneously, this will likely not be the case here due to limited resources or budgets. By prioritizing tasks, you will be able to more efficiently work through line items.
Likelihood of occurrence
Items should be ranked on their likelihood of occurrence. These rankings will be highly dependent on both the individual line items as well as the unique security posture of your business. Realistically assess the possibility of given threats based on shared industry knowledge and historical company data.
Severity of potential impact
Each item on your list should be given a ranking based on the potential the item has to disrupt your business. This can include operational delays, financial setbacks, or other metrics deemed crucial to day-to-day business.
Risk impact designation
The risk impact of each item on your list is a subjective evaluation of each item’s priority on your list. This column should weigh the potential severity of a threat with its potential likelihood. Items with high likelihood and high severity should be near the top of your list. Conversely, items with low likelihood and low severity should be near the bottom of your list. All other items will fall somewhere in between, and you will need to identify your course of action based on these items.
Actionable steps
Information in a risk assessment is ineffective unless it is acted upon. Your risk assessment template should include next steps for addressing concerns that have been identified.
Identify actionable steps to remedy risks
For each line item, begin listing what can be done to remedy the situation and reduce or eliminate both the severity of information breach as well as its likelihood of occurrence. While you may not be able to completely eliminate all organizational threats, working toward more secure solutions is still an effective use of resources. Never let perfect be the enemy of good.
Designate a champion to address the risks
Each line item should have a responsible party in charge of seeing actionable steps through to completion. While recognizing threats and creating action plans are both effective first steps, only by giving an individual or multiple individuals the authority to execute plans can real change be enacted.
Additional Considerations
The steps above will cover a large portion of your risk assessment template. However, there may be special circumstances particular to your industry or organization that you also want to consider. Create a section of your assessment to include comments or feedback that encourage productive communication around each topic. Additionally, you may want to include workflows for reviewing and assessing outcomes to ensure followthrough on any and all actions taken.
A template will give your organization a starting point to work from. Always update and adjust the template as your organization works through audits. This will allow for continued improvement of processes.
GLBA audit checklist
If you have compliance concerns, you can start addressing them by studying and understanding the three parts of the GLBA, then planning your compliance for each section. Doing an audit of your organization’s data can help you identify vulnerabilities and locate where security needs to be implemented to secure the NPI and other sensitive information.
Consider using a tool that can scan on-premise and cloud databases, looking for instances of customer names, addresses, social security numbers, payment information, and other nonpublic data that could be at risk. From there, you can expand your software use to include task automation and streamlined reporting.
This GLBA compliance checklist can help you perform your audit and bring your organization fully in line with the requirements of the GLBA to prevent your institution from suffering the hefty consequences that accompany non-compliance. Businesses may face fines up to $100,000 per violation, while each individual involved in non-compliance can be liable for fines up to $10,000 per violation or up to five years imprisonment.
GLBA compliance and data privacy
GLBA compliance and data privacy are connected at multiple levels. These two areas often overlap with the need to know where sensitive data resides and classifying all data to understand permission, usage and sharing at a glance.
Data collection and storage
How your institution collects and stores customer data must be aligned with the overarching goal of preventing unauthorized access and protecting consumer privacy. Without proper safeguards in place that address the path data takes in your institution, and where or how it is held, GLBA violations aren’t just possible—they are likely.
Data usage and sharing
How your institution uses and shares data must be clearly disclosed, and third parties must be held to the same standards as your own organization. Data cannot be used by an institution or its employees outside of the clear agreement with the consumer, and the consumer must be given the right to opt-out of data sharing with third parties to satisfy the Fair Credit Reporting Act (FCRA).
Data protection and security
How your institution protects data security and privacy must be detailed in a written plan and updated regularly. Employees must also receive appropriate training at regular intervals to ensure they remain aware and alert for social engineering attempts at accessing sensitive information.
Data compliance is easier with a data compliance tool that can help classify information as it enters your database, partition the data, and apply parameters designed to keep the handling of the data compliant with the GLBA and Fair Credit Reporting Act.
Data privacy safeguards help keep financial institutions in compliance by making sure that:
- You know where sensitive data resides at all times, whether on-premise, in the cloud or both places.
- All types of sensitive information or correctly identified and classified for better compliance across the board.
- Sensitive information is adequately protected both where it resides and where it is passed during allowed sharing, including on endpoint devices as they pass in and out of your physical network
An added benefit of GLBA compliance is the relationship your institution will build with your consumer and customer bases. When you provide clear disclosures and opt-outs, are transparent in your use of data and sharing practices, and put internal safeguards in place to prevent data from being vulnerable to pretexting, you create a culture of security and respect for privacy. The result is a higher level of trust and confidence in your institution from your target demographics.
