Everything you need to know about endpoint security
Endpoint devices made the initial mass shift to working remotely a relatively seamless process for enterprises in terms of keeping business operations functioning as normal, but the access to sensitive data these devices can provide makes them ideal targets for cyberattacks. This, compounded with the emerging permanence of remote work environments, has made the need to properly monitor endpoint devices more urgent than ever.
What is endpoint security?
Endpoint security is the process of securing devices like computers and mobile gadgets using a variety of methods to ultimately protect the sensitive data these devices either store or have access to. Endpoints can provide entry into an enterprise’s network, and in turn, its data, making them frequent targets of cybersecurity threats.
What are endpoints?
An endpoint is any device that can access an enterprise network. This includes desktop and laptop computers, smartphones, tablets, smart watches, printers, servers, ATM machines, medical devices and smart home technology. The list is ever-expanding, making it harder for IT teams to keep track of everything and contributing to why endpoint security so often falls to the wayside.
Because of the prevalence of remote work, laptops are the most common endpoint targets for cybersecurity attacks and need to be protected in order to ensure that remote work is done securely.
Why do endpoints need protection?
Nowadays, data is extremely valuable to enterprises. It’s used for both day-to-day functions and informing business strategies and decisions, which can shape the future of an organization. A data compromise of any sort could severely impact business operations.
Not to mention, much of the data that enterprises regularly collect and use consists of highly sensitive, personally identifiable information (PII), which are subject to a plethora of data privacy laws mandating its security. So, ensuring sensitive data is protected wherever it exists — including endpoint devices — throughout all stages of its lifecycle is a legal requirement that could result in costly penalties if not complied with.
To better illustrate why endpoints need to be secured with multiple lines of defense, here’s an example: Let’s say a remote employee who’s authorized to access highly sensitive data for work downloads and saves a file of it from the cloud to their laptop. After completing tasks for which the data was needed, the employee forgets to delete the data from the laptop and heads to a cafe to finish working. Now, the employee is working off a public network on a device that likely doesn’t have password-protected access (and if it does, it’s probably something that can be easily guessed). Not only can the data on the device be easily compromised, but access to the cloud where much more data exists is readily available to be misused.
Endpoint security risks
In addition to the obstacles created by remote work environments, other endpoint security challenges include digital transformation initiatives, switching to cloud-based services, human negligence and inconsistent security measures across devices. These can all unlock the door to cyber threats, namely:
- Phishing scams, which occur when a fraudulent communication is sent to recipients disguised as a trusted source, such as a bank or online retailer. The message, often an email or text, lures recipients into giving away sensitive data, usually by clicking a link or downloading an attachment. While a phishing scam can be executed as a standalone attack, it can also be part of a larger attack strategy to deliver malware.
- Drive-by downloads, which occur when an unsuspecting user accesses an insecure website where malicious script has been planted, triggering a download of malware and infecting the device.
- Credential theft, which involves stealing usernames and passwords to gain access to an organization’s data for malicious purposes. These credentials can be obtained through a phishing scam, but they can also be compromised simply because they’re weak, which is why strong passwords and multi-factor authentication are important components of endpoint security.
- Ransomware, which is malware that renders an organization’s data entirely unusable until a ransom is paid. It can be delivered to endpoint devices in a number of ways, including through phishing scams or seemingly harmless game or application downloads.
- Insider threats, which are exactly what the name implies — a threat that comes from inside an organization. These can be accidental, resulting from employee negligence, or deliberate, where someone on the inside either collaborates with an outside malicious source or is the malicious source posing as a harmless employee.
How have endpoint security risks evolved in a post-COVID world?
The COVID-19 pandemic accelerated the shift to remote work without much consideration for the devices that work would be conducted on. Employees were still accessing, using and sharing data to do their jobs, but without the protection of secure networks and devices. The door for cyberattacks was not only left unlocked, but wide open. IT and governance teams scrambled to implement strategies to mitigate data privacy risks stemming from expanded IT perimeters and greater amounts of data in transit than ever before.
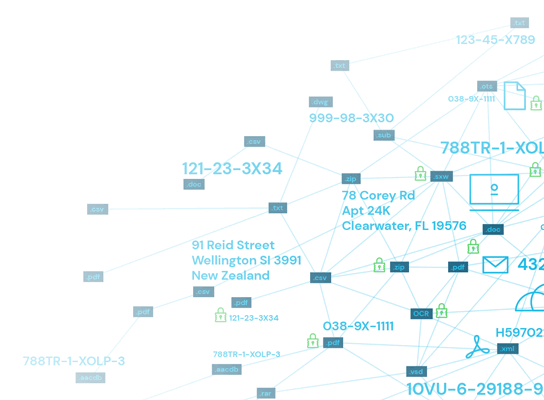
They also had to take into consideration that this data wouldn’t just be moving across company-issued hardware anymore. Operating systems, apps, networks and other endpoints not owned, operated and secured by company data privacy tools were involved now as well, making data discovery even more complex. Without complete data visibility, there’s a chance of it going unprotected, leaving it vulnerable to threats and violating data privacy laws.
As remote work becomes more common within organizations, IT and governance teams face the ongoing challenge of developing a long-term approach for monitoring and protecting broad networks of endpoints and all the data existing within them — much of which is unstructured and already difficult to discover and manage.
What does endpoint security look like?
Endpoints need to be secured at device, network and cloud levels. In addition to device-level safeguards like strong passwords, multi-factor authentication, antivirus software and data encryption, an enterprise endpoint security plan should include network access controls and cloud protection like firewalls, virtual private network (VPN) connections, threat-detection software and sensitive data discovery tools that accurately locate sensitive data anywhere it exists across endpoints and the cloud services they’re connected to and immediately protects it.
It’s important to remember that these security measures must be used in tandem with one another and not as standalone solutions. Breakthrough cyberattacks are always possible, and the best way to ensure minimal disruption is by having all lines of defense in place.
Data loss prevention for safer data and more secure endpoints
A comprehensive data loss prevention (DLP) program helps enterprises identify data loss risks, understand and manage those risks and prevent data loss. DLP programs also help uphold regulatory compliance. They enable organizations to go beyond implementing arbitrary, potentially ineffective security measures by providing visibility into exactly what needs to be secured so it can be in the most efficient way possible. Basically, an endpoint DLP plan can better inform your endpoint security strategy to maximize its efficacy.
Sensitive data discovery enhances endpoint security
Because they can house high volumes of sensitive data, endpoint devices must be equipped with a tool that’s constantly discovering sensitive data wherever it lives so these endpoints can be secured on the most granular level.
A common issue with endpoints is that they can unknowingly be home to duplicate or outdated data, which then goes unprotected and becomes a security risk. This also directly violates data privacy laws. Regulations like the GDPR and CCPA mandate that certain data can only be stored for as long as it’s needed for its originally intended purpose. Once data is no longer useful, it needs to be disposed of. But, if a secondary version of that data exists on an endpoint device unbeknownst to an organization, it’s considered noncompliance and becomes a vulnerability cyberattackers can exploit.
Privacy laws also permit data subjects to be forgotten by requesting to have their data entirely deleted. Organizations must fulfill that request within a specific timeframe to remain compliant. Again, if duplicate versions of that data are unknowingly stored on endpoint devices, it won’t be deleted, the data subject’s request won’t be honored, and all this will lead to costly penalties.
Sensitive data discovery, as part of an endpoint DLP plan, finds all at-rest data on endpoints and identifies any discrepancies so they can be properly remediated — another prime DLP component — reducing potential cybersecurity vulnerabilities and noncompliance risks while enhancing overall endpoint security.
How Spirion can help you secure endpoints
To best protect their organization’s endpoints, IT teams need a clear understanding of both endpoint and data inventory to know which devices pose the highest risks, how to protect different types of data on these devices and identify potential vulnerabilities in security architecture. Once all this is clear, a plan must be implemented to actively monitor these devices and their data, but as companies grow and remote work environments become permanent, this plan needs to include automation as part of that monitoring strategy.
That’s where Spirion comes in. Our Sensitive Data Platform can find anything with 98.5% accuracy and the lowest false positive rate in the industry. This includes any sensitive data located offline, on endpoints and in cloud repositories. Additionally, Spirion’s discovery tools use context-aware sensitive data detection and purposeful classification to automatically identify, quantify and manage areas of privacy risk across every instance where the data resides.
Properly secured endpoints are an essential component to any enterprise’s overarching data security strategy, but this can only be effectively achieved by starting with accurate, automated sensitive data discovery.
