You’ve made the decision to protect the data privacy and security of your colleagues, customers, and community. Now the hunt begins for the right software to manage all of your sensitive data, keep you compliant, and remediate risks. However there are more than 300 data privacy software companies to choose from according to the International Association of Privacy Professionals (IAPP), making the process
What is data privacy management software?
A data privacy management software solution ensures sensitive and private information collected by your organization can be properly discovered and classified according to regulations like the General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), and the Payment Card Industry Data Security Standard (PCI DSS).
Five years ago, 43% of all business information was stored online. As of 2022, that number has risen to 60% and is trending to rise even higher. This data includes personally identifiable information (PII) like Social Security numbers, credit card numbers, or private addresses capable of being linked directly to a single individual.
As more organizational records are stored online, sensitive information faces an increased risk of unauthorized access, meaning it’s more important than ever for businesses to implement effective data protection strategies. Your data privacy management software should be able to accurately find and classify data, as well as reduce and manage your exposure risks.
Why implement a data privacy management solution?
Proper data discovery and classification are essential for good data hygiene. More importantly, failure to practice good data hygiene can result in significant legal and financial ramifications for organizations that are noncompliant with regulations. At the same time, new rules proposed by the SEC would make proper data discovery, classification, and remediation tools even more important for organizations collecting and storing sensitive data, lest they face increased scrutiny and consequences in the event of a data breach.
How to select a data privacy management software
To select the best data privacy management tool for your organization, it’s important to understand how the software will improve your compliance posture and reduce the risks associated with a data breach. Here are the key areas to consider when reviewing your software options.
Does it offer a clear picture of your entire data landscape?
Every organization holds sensitive data, but most organizations don’t know how much they have, where it is stored, or how it is structured. In other words, their data landscape is scattered and hidden. Before you can take any real steps to be in compliance with data privacy laws, you have to be able to locate all of your data.
The data privacy management software you choose should be able to locate both structured and unstructured data across your network, cloud systems, and apps. It should also cover all endpoint devices, including internal networks and remote work or work from home settings.
Does the data privacy tool provide automated discovery and classification capabilities?
Organizations often struggle with their data classification programs because they approach them mostly as manual processes. However, classifying data manually is too labor-intensive, time-consuming, and error-prone to be a practical solution for all but the smallest companies. In particular, manual data classification suffers from the following issues:
Inaccuracy — Busy employees often fail to classify data at all or simply pick the first tag in the list to expedite the process.
Inconsistency — Different people classify similar documents in different ways.
Inflexibility — As companies’ sensitive-data requirements and regulations change, no one has the time or inclination to update the tags on terabytes of existing data.
Failure — As users realize that data is not classified correctly, they will quit trusting the process and the whole project fails.
Automating data classification overcomes these limitations by making the process reliable, accurate, and continuous. A sophisticated platform can spot personally identifiable information (PII) by looking for data patterns, as well as using content and context clues, to find names, dates of birth, addresses, phone numbers, financial information, health information, and social security numbers accurately. Additionally, automated systems can also re-classify data as needed, such as for updates and changes within the business or from changes in compliance regulations.
Does the software enable compliance with data privacy laws and standards?
Organizations in nearly all industries will face governing bodies, internal audits, and mandates with which they must comply. Combine these industry compliances with other data privacy standards and regulations, and you have a virtual alphabet soup of regulations to follow. What makes some of these laws so difficult is that none of them follow the same script. Although they share a similar intent of protecting consumer data, the details, timing, required responses, and penalties vary widely, making compliance increasingly difficult.
This is where you should have the highest expectations of your data privacy software. The best solutions available will sort out the confusion behind different privacy regulations, as well as produce Data Subject Access Requests (DSAR) and Subject Rights Request (SRR) request information that demonstrate protection.
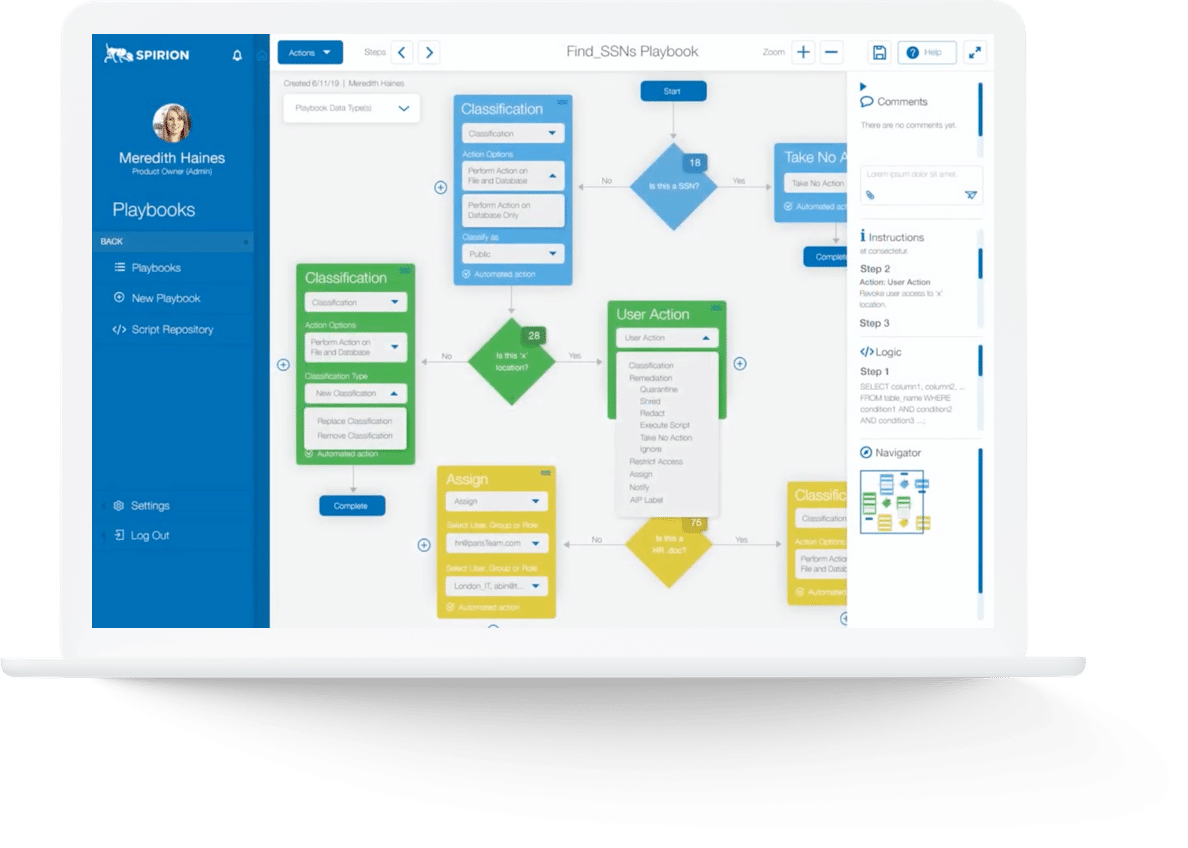
Can the data privacy management software model and run complex conditional workflows?
To enforce data privacy and retention policies, your software should automate workflows to create efficiencies and avoid human error in data discovery, classification and remediation.
Workflows provide the ability to assign results to users based on user defined criteria, send notifications when automatic or manual assignment occurs, apply remediation actions, track status, and assign classifications. However, many automation tools follow a convoluted process with an unintuitive design that’s difficult to audit and prone to errors and omissions. You’ll want to make sure your data privacy software features an easy-to understand user interface that allows you to clearly model a complete data privacy lifecycle from discovery to remediation, with detailed controls over actions and decisions at each step.
Does the software provide a reliable dashboard and advanced reporting and analytics?
People are the most powerful tool in any organization’s security and privacy strategy and empowering them with knowledge is the key to the strategy’s success. Choose a data privacy software solution that offers a comprehensive dashboard with visual tools to communicate clearly and accurately what’s happening within your data ecosystem.
Having a reliable dashboard arms your security team with the insights it needs to stop a potential data incident and risk. You need the ability to present information to your organization’s top leadership, especially in the case of a breach. Advanced reporting and analytics can provide system-level overviews and an in-depth drill-down into sensitive data scan results to guide remediation policies and practices.
Can the data privacy tool quickly and effectively handle remediation when a risk is found?
When a data security problem is found, quick action is required to address it. Your data security software should offer a broad range of remediation actions. It may need to fix corrupt or inaccurate records by replacing, modifying or deleting them. With the help of complex conditional workflows and an automated data classification policy, it “knows” which action to take in a specific situation. It may shred, redact, quarantine, encrypt, or take other actions – which is especially important for privacy compliance, as it prevents data from being repeated and hidden throughout the network. Rapid and automated remediation can save time, money, and storage space while also reducing legal and regulatory risks.
Why Spirion’s Data Privacy Manager is your best-of-breed solution
While some tools provide a few of the requirements we’ve been talking about, only Spirion’s Data Privacy Manager (DPM) offers them all.
Find anything, anywhere
Spirion’s Data Privacy Manager allows you to search locations such as PDFs, images and spreadsheets to cloud repositories, databases and even your colleague’s laptops. Wherever sensitive data lies, we promise to find it.
Highest accuracy in the market
Spirion’s AnyFind technology goes beyond pattern matching in its discovery and uses context and content clues to find sensitive data, with less than 2% false positives.
Automated classification and real-time remediation
DPM automates data classification and enables it to persistently follow the data wherever it goes. It offers real-time risk remediation so that as data comes into your enterprise it can be trained and controlled. With more remediation options than anyone else in the market, DPM can offer optimal protection with limited business disruption.
Real-time risk remediation
Spirion’s Data Privacy Manager offers real-time risk remediation so that as data comes into your enterprise it can be trained and controlled. With more remediation options than anyone else in the market, Data Privacy Manager can offer optimal protection with limited business disruption.
Easy-to-use playbooks
DPM recently released playbooks to make classifying and controlling your sensitive data easier. Rather than having a team to write complex scripts to classify and control your data, you can build a playbook that follows those same complex and conditional workflows in a simple and easy-to-use interface.
Defend your organization’s data
Spirion’s Sensitive Data Platform offers unmatched accuracy to protect your data. With 98% accuracy, this solution helps you discover data no matter where it resides, automates workflows, and catalogs your data for more efficient access. To see the platform in action, contact us today. Our experts can address the security needs of your organization with scalable solutions and a data-centric approach to privacy and security.