What is the GDPR?
- How did the GDPR come about?
- What are the seven principles of the GDPR?
- What is considered sensitive personal information under the GDPR?
- What companies are affected by the GDPR?
- Who is responsible for ensuring compliance?
- What is GDPR compliance?
- How is the GDPR enforced in the US?
- What are the fines for GDPR non-compliance?
- What has the GDPR changed?
- What US data regulations and privacy laws were inspired by the GDPR?
- How Spirion can help you achieve GDPR compliance
The General Data Protection Regulation (GDPR) is the leading data privacy legislation within the European Union and one of the toughest in the world. It took effect on May 25, 2018, and its rules give EU citizens greater control over their personal data while requiring controllers and processors of that data to properly protect it or face massive financial consequences. GDPR compliance is not restricted solely to EU businesses; any entity collecting data from EU citizens is subject to the GDPR’s rules and penalties.
Under the GDPR, data subjects have the right to:
- Access and inquire how their personal data is being used.
- Have their data deleted if they’re no longer customers or simply don’t want their data being used by a company anymore.
- Transfer their data to a different service provider.
- Consent to the gathering of their data.
- Make adjustments to their information in the case it’s incorrect or out of date.
- Restrict use of their data for marketing purposes, meaning the moment the request to cease is received by an organization, it’s honored.
- Be notified of any compromises or breaches affecting their personal data within 72 hours of an organization becoming aware that a transgression has occurred.
How did the GDPR come about?
In 2012, the European Commission recognized a need for reformed data protection legislation across the EU. The goal was to better equip European countries for the digital age, as previous data privacy laws didn’t account for technological advancements such as mobile devices, cloud computing or social media. The EU Commission also recognized that the digital age would be powered by personal data, and in order to grow the digital economy, consumers needed some sort of control over their data as well as assurance that it would be protected from misuse. Enter the GDPR, which was agreed upon in April 2016 and officially put into action in May 2018.
What are the seven principles of the GDPR?
The GDPR contains seven principles relating to how personal data is processed that must be upheld. These principles are as follows:
- Lawfulness, fairness and transparency – This means there must be a valid basis for collecting personal data. The data must then only be used for the reason(s) clearly and honestly communicated to individuals prior to sharing their information. They should not feel misled by how you use their data.
- Purpose limitation – The purposes for processing personal data should be apparent to individuals from the start and documented in privacy notices. This data can only be used for a new or different reason if it serves the same purpose as the original, you’ve received updated consent or are legally required to.
- Data minimization – You should only collect the necessary relevant data to fulfil your stated purpose of use. Don’t collect more than you need because you think it might be useful one day.
- Accuracy – If any data you possess is identified as incorrect or misleading, it should be promptly disposed of. To ensure this, you will need to have measures in place that can keep the data updated and accurate.
- Storage limitation – Data cannot be stored for longer than it’s needed. When outlining how you plan to use personal data, you will also need to specify the length of time it needs to be kept, as well as justification for that timeframe. When the retention window expires, data must be securely erased.
- Integrity and confidentiality – Also known as “the security principle,” this ensures you have proper security measures in place to protect all the sensitive data you collect and store.
- Accountability – You are responsible for how you use the data you collect, how you comply with other principles and how you document your compliance.
What is considered sensitive personal information under the GDPR?
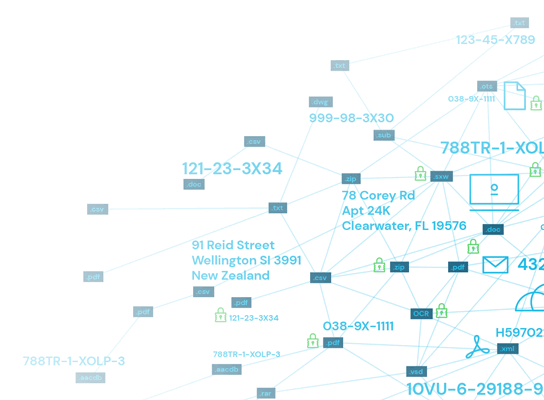
Personal data under the GDPR includes anything that can uniquely identify someone, such as names, home addresses, social media handles, IP addresses, race, ethnicity, political affiliation or sexual orientation, as well as health, genetic and biometric data.
What companies are affected by the GDPR?
Companies that have a business presence in any EU country, as well as companies that do not have a business presence in the EU, but do process data from citizens in the EU, are required to comply with the GDPR and its seven principles for processing personal data.
Who is responsible for ensuring compliance?
The GDPR defines the three primary roles responsible for ensuring compliance as controllers, processors and data protection officers.
Controllers and processors
- Controllers determine the purpose for collecting personal data and how it will be used.
- Processors then use that personal data on behalf of the controller, based on the controller’s instructions. Oftentimes, processors are third-party entities.
To better understand the controller and processor roles in practice, take this example: A clothing company enlists a direct mailing service to send postcards with discount codes to customers’ homes for their birthdays. In this scenario, the clothing company is the controller, as it determines the purpose for collection and use of customers’ personal information, while the processor, the direct mailing service, simply handles labeling and sending the postcards as the controller instructs.
While the GDPR pins sole responsibility for breaches or noncompliance on processors, both controllers and processors will be equally liable for the fines and penalties that result from a violation. Because of this, existing contracts between controllers and third-party processors need to be revised to explicitly define how personal data will be processed and protected, as well as how a breach will be reported in the unfortunate event of one, to meet GDPR compliance standards.
Data protection officers
- Data protection officers (DPOs) are appointed by controllers to oversee GDPR compliance within an organization and its overall security strategy. Organizations must have a DPO if they process large quantities of “special” EU citizen data, regularly monitor data subjects on a large scale or are public authority.
If the clothing company in our earlier example were to track how its customers behave while shopping online (i.e. monitoring what they search for, add to their carts and purchase) with the intention of providing better product recommendations and an improved eCommerce experience, a DPO must be appointed, as this is considered regular monitoring of data subjects.
What is GDPR compliance?
To be compliant with the GDPR, organizations must be able to:
- Accurately identify all personal data under their control.
- Give data subjects access to their personal data.
- Maintain data security.
- Notify authorities of data breaches.
- Police third-party processing of personal information.
- Keep timely and accurate records of data protection activities.
Of course, each of those requirements can’t happen on their own; there are steps that need to be taken to achieve them. Let’s take a closer look at what it really means for an organization to be GDPR-compliant.
How to become GDPR-compliant
For U.S. companies, the GDPR created a handy checklist that will first help you determine whether the law is even applicable to your data, and if it is, what must be done to comply.
- Audit your data to understand your liabilities. This will allow you to know whether you possess any personal data from EU citizens, thereby requiring you to comply with the GDPR. By being aware of all the sensitive information your organization owns, you can determine which other data privacy regulations you’re subject to comply with as well.
- Get consent from customers for data processing. Let customers know why you’re wanting to collect their data and how you plan to use it, as their consent is required for you to move forward with processing.
- Assess your data privacy risks and processes. This allows you to understand potential security risks to your data so you can implement safeguards that will reduce the chances of these risks materializing. You’ll also be able to identify any vulnerabilities in your existing security infrastructure to ramp up protection.
- Create or update data processing agreements with vendors. Data controllers will be held responsible for compliance infractions made by their processors. To help avoid this, controllers should explicitly state the rights and responsibilities of both parties in a data processing agreement.
- Appoint a DPO. A data protection officer oversees an organization’s GDPR compliance and serves as an expert resource for all things concerning data protection laws. As previously discussed, there are certain scenarios where a DPO is mandatory and not having one can result in severe fines.
- Designate an EU representative. The GDPR requires this for businesses without a physical presence in the EU in order to keep a close eye out for noncompliance. If a violation of compliance occurs, this representative would be the one issuing penalties.
- Prepare for a data breach. This is not to say there will be one, but in case it happens, you’ll be prepared. Having data duly fortified by strong encryption can reduce the severity of fines, as well as your notification obligations.
- Be aware of laws affecting the transfer of data across borders. The GDPR allows data transfers to countries outside of the EU, but those countries must have their own data protection regulations in place.
Three ways to maintain compliance as GDPR evolves
1. Create a culture of awareness
It’s essential that your organization trains all individuals, even those who don’t touch any sensitive data, about data security responsibilities and GDPR principles. Everyone should be aligned when it comes to data privacy procedures; many compliance violations happen because of simple human error.
2. Implement a data protection plan
To uphold the GDPR’s security principle, you need a privacy framework that safeguards all of your organization’s sensitive personal information from the moment it’s created, as it moves through your organization and finally when it’s time to be destroyed. Of course, properly protecting your data starts with knowing it exists, what it consists of and where it lives. From there, it can be sorted and secured accordingly, automatically checked for accuracy and safely erased when it hits its expiration date.
In short, a data protection plan is essential for compliance, and having data lifecycle management tools for sensitive data discovery, data classification and remediation as part of that plan will allow you to remain compliant as both your organization and privacy laws scale up.
3. Document everything thoroughly
A breach response plan you can rapidly enact is key to minimizing the GDPR penalties you could incur as a result of a breach. To identify the source of the breach and assess what data was impacted, proper documentation of who has access to what data, when they access it and how they use it has to exist. Breach reporting must be done in a timely manner in order to comply with the GDPR, and thorough documentation is what will help you achieve that.
How is the GDPR enforced in the US?
International enforcement of the GDPR can be handled a few different ways depending on whether an organization has a presence in the EU or not. For those with a presence, their assets — bank accounts, real estate or servers — can be seized in the event of a noncompliance violation.
The GDPR requires organizations that don’t have a presence in the EU to appoint a representative who does. This individual would be responsible for imposing penalties in the event of noncompliance. GDPR practices can also be enforced outside of the EU via international law. National enforcement agencies would provide mutual assistance to each other in the form of notifications, complaint referral, investigative assistance and information exchange to ultimately support the enforcement of each other’s privacy regulations.
What are the fines for GDPR non-compliance?
The GDPR has bolstered its enforcement by implementing severe financial penalties for noncompliance and violations. Previous EU data laws did not have as stringent enforcement tactics as the GDPR does now.
GDPR fines are broken up into two tiers based on infringement severity:
- Lower-tier fines for less severe infringements, which are typically violations of the articles governing controllers, processors and DPOs.
- Higher-tier fines for more severe infringements, which are violations of the articles governing the basic principles of processing data, conditions for consent, data subjects’ rights and international or third-party transfers of data.
Less severe infringements can result in fines as high as 10 million euros (nearly $12 million) or 2% of an organization’s global annual turnover, whichever is greater. More severe infringements can result in fines as high as 20 million euros (nearly $24 million) or 4% of an organization’s global annual turnover, again, whichever is greater. Data protection agencies can also impose their own fines, however, these are significantly less expensive.
Currently, Google holds the title for the most expensive GDPR noncompliance fine ever issued. In 2019, French regulator CNIL fined the tech giant nearly $55 million for not properly disclosing how it collected user data across its services and used it for personalized advertisements.
This is an extreme case; not all infringements will be fined the maximum amount. The criteria to determine specific fines considers the gravity and nature of the infringement, the precautions involved to uphold GDPR compliance and the personal data affected in the infringement, as well as whether the infringement was intentional or a result of negligence, whether there were actions taken to mitigate its damage, whether the perpetrator had any previous infringements and whether the perpetrator cooperated with authorities to resolve the infringement.
What has the GDPR changed?
Since the introduction of the GDPR in 2018, many news sites, social media platforms and tech firms have felt the brunt of its strict legislation, most notably in the form of lost advertising revenue from the EU. Naturally, as website cookies can’t inconspicuously gather, use and sell data like they used to, companies in every industry have had to scramble to find new and more importantly, compliant, ways to market and connect with audiences. The uncompromising enforcement and hefty fines affiliated with the GDPR have given entities no choice but to come to terms with data privacy. Some are even attempting to embrace it.
Perhaps the GDPR’s biggest impact can be best seen in the ongoing global creation and implementation of data privacy reform and regulation. Just as the GDPR altered the world of big data by finally prioritizing the privacy of data subjects, your organization must prioritize compliance to move forward in the digital age.
What US data regulations and privacy laws were inspired by the GDPR?
The California Consumer Privacy Act (CCPA), the most comprehensive U.S. state-level data protection law regulating what businesses can do with personal information collected from California residents, can credit the GDPR as its inspiration. The CCPA allows any California consumer to request full visibility into how their personal data is used and shared.
Like the GDPR, the CCPA protects a broad scope of data and is not limited to one industry or business sector. Also like the GDPR, the CCPA requires entities collecting data from California residents, even those without a physical business presence in the state, to comply with its rules.
The CCPA was formally enforced in July 2020, but by November of the same year, California lawmakers were already giving it a facelift, moving the state’s data protection legislation even closer to the GDPR with the passing of the California Privacy Rights Act (CPRA). While it won’t go into effect until 2023, the CPRA calls for more detailed data inventories, updated risk assessments and additional access controls.
As the most populous state and a powerful player in U.S. economic and political spaces, what California says, goes. At least states like Nevada, Virginia and Florida agree, as proven by the passing of Nevada’s Senate Bill 220 in October 2019, Virginia’s Consumer Data Protection Act in March 2021 and the almost-passing of Florida’s House Bill 969 in April 2021. It’s worth noting HB 969 is the closest Florida’s ever been to implementing data privacy reform — one can assume lawmakers won’t give up just yet. And, many other states have followed suit, albeit on a smaller scale to start.
How Spirion can help you achieve GDPR compliance
To ensure your organization complies with the GDPR, as well as all the current and future state-level regulations to come, turn to Spirion. Our Sensitive Data Platform’s powerful discovery capabilities identify personal data wherever it resides across your enterprise and automatically classifies it to assist in the development of a comprehensive data inventory. Our SDP promotes data-at-rest security and provides a management dashboard that enables organizations to execute their data protection programs, making it simple to comply with even the strictest data privacy regulations.
